Why an Enterprise Data Access Control Model Is Critical for Modern Analytics Platforms
As enterprises scale AI, real-time analytics, and domain-driven data architectures, security complexity grows faster than data volume.
Fragmented access controls across storage, SQL engines, Spark workloads, and reporting layers create governance blind spots, compliance risk, and operational overhead.
For organizations modernizing their analytics stack, the real question is:
How do you enforce consistent, auditable access control across every workload — without multiplying permission systems?
This is where unified security architecture becomes foundational.
Reading insights: Read further on how to transform your data migration into a catalyst for AI-driven growth with our data migration services.
How a Unified Enterprise Data Access Control Model Eliminates Fragmented Security
In traditional architectures:
- Storage permissions are managed independently
- SQL roles are configured separately
- Spark or notebook-level access is defined elsewhere
- BI tools apply their own row-level controls
These siloed controls introduce policy drift.
A unified enterprise data access control model reduces these silos by centralizing identity-driven enforcement. A dataset restricted at the warehouse layer may be unintentionally exposed via another compute path.
| Dimension | Fragmented Model | Enterprise Data Access Control Model |
|---|---|---|
| Identity | Decentralized | Centralized |
| Enforcement | Layer-specific | Cross-workload |
| Auditability | Limited | Unified logs |
| AI Security | Inconsistent | Consumption-time enforced |
For organizations operating under regulatory scrutiny, this creates:
- Inconsistent enforcement
- Audit complexity
- Increased data leakage exposure
- AI governance gaps
To understand how governance frameworks reduce enterprise risk, explore our article on building an enterprise data governance operating model- Data Governance For Data Quality
Building an Enterprise Data Access Control Model with Centralized Identity
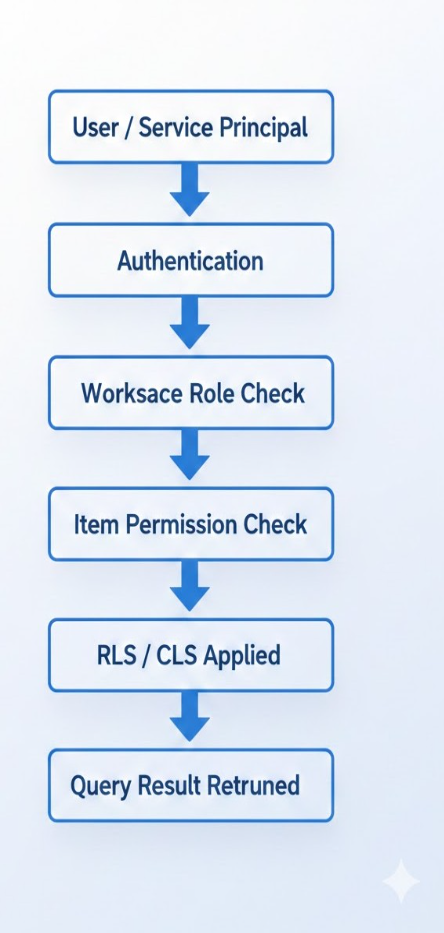
A scalable enterprise data access control model integrates:
- Identity-based authentication
- Workspace boundaries
- Item-level permissions
- SQL endpoint roles
- Row-level security
- Column-level security
Centralized identity ensures that every access request is evaluated against a single policy framework.
Fragmented vs Unified Security Model
| Dimension | Fragmented Architecture | Unified Security Model |
| Identity Management | Multiple systems | Centralized identity |
| Policy Enforcement | Engine-specific | Cross-workload |
| Policy Drift Risk | High | Controlled |
| AI Workload Governance | Inconsistent | Consumption-time enforcement |
| Auditability | Dispersed logs | Central traceability |
OneLake as the Foundation of Centralized Enforcement
A unified storage foundation enables consistent access evaluation across workloads.
Instead of managing disconnected permission models, enterprises can align:
- Identity-based authentication
- Workspace-level boundaries
- Item-level access permissions
- SQL endpoint roles
- Row-level and column-level controls
This design supports a centralized data lake security model while maintaining workload flexibility.
For architectural context, read our breakdown of Microsoft Fabric Architecture: A CTO’s Guide to Modern Analytics & AI.
Applying an Enterprise Data Access Control Model to Mirrored and Replicated Data
Replicated datasets must be governed within the analytics environment.
An enterprise data access control model ensures that mirrored data is secured using:
- Item permissions
- Row-level security
- Column-level security
- Workspace roles
Mirroring enables operational systems to replicate data into analytics environments for AI and reporting.
However, replication does not transfer security automatically.
Once data enters the analytics environment, it must be governed using native access controls such as:
- Row-Level Security (RLS)
- Column-Level Security (CLS)
- Workspace roles
- Item permissions
| Control Layer | Purpose | Enforcement Point |
| Workspace Role | Boundary control | Project scope |
| Item Permission | Dataset restriction | Object-level |
| SQL Role | Query authorization | Execution engine |
| Row-Level Security | Record filtering | Query result |
| Column-Level Security | Sensitive attribute restriction | Query result |
Why Consumption-Time Enforcement Strengthens an Enterprise Data Access Control Model
A critical shift in modern security models is consumption-time access evaluation.
Instead of relying solely on storage-level permissions, policies are evaluated at query execution.
This applies when data is accessed via:
- SQL endpoints
- Notebooks
- Warehouses
- Reports
- AI training and inference workloads
Enhance your analytics outcomes and turn fragmented data with our data engineering solutions and MS Fabric capabilities.
Securing AI Workloads with an Enterprise Data Access Control Model
AI notebooks and inference pipelines must operate under the same identity-based framework.
An enterprise data access control model ensures:
- AI training datasets remain governed
- Sensitive attributes remain protected
- Service principals follow least-privilege access
- Logs capture AI-driven data access events
This is essential for enterprise AI governance strategies.
Governance and Compliance Benefits of an Enterprise Data Access Control Model
Regulators increasingly require demonstrable enforcement — not just documented policy. Modern enterprise security architectures increasingly align with Zero Trust principles, where access decisions are continuously evaluated based on identity and context. The NIST Zero Trust Architecture framework outlines this model in detail and reinforces why an enterprise data access control model must evaluate permissions at consumption time rather than relying solely on perimeter-based controls
Unified enforcement enables organizations to trace:
- Who accessed the dataset
- Through which workload
- Under which identity
- At what time
This level of traceability strengthens:
- Internal compliance programs
- Risk management posture
- Security audit readiness
Explore the best practices, architecture, and governance principles that power enterprise-grade data quality frameworks in our blog.
Common Security Risks Without an Enterprise Data Access Control Model
Organizations without a unified enterprise data access control model face:
- Shadow data copies
- Conflicting permission layers
- Inconsistent row-level enforcement
- AI bypassing reporting restrictions
- Manual audit tracking
Embedding the enterprise data access control model into platform architecture eliminates these risks.
Addressing these issues requires a unified access model embedded into architecture — not layered later.
Operating Model Considerations for an Enterprise Data Access Control Model
A well-designed enterprise data access control model balances governance and agility.
- Platform teams define guardrails
- Domain teams operate within boundaries
- AI teams consume governed datasets
- Security teams monitor centralized logs
Security becomes embedded into architecture rather than layered on later.
Techment’s perspective on Fabric AI Readiness: How to Prepare Your Data for Scalable AI Adoption provides a practical blueprint.
Conclusion
As enterprises expand AI, real-time analytics, and domain-driven architectures, fragmented access control models become unsustainable.
A unified security framework built around centralized storage, identity-driven permissions, and consumption-time enforcement provides:
- Consistent policy enforcement
- Reduced governance overhead
- Stronger auditability
- Secure AI enablement
Unified analytics security is no longer optional — it is foundational to scalable innovation.
FAQs
1. What is a unified enterprise analytics security model?
A centralized access control framework that enforces identity-based policies consistently across storage, compute, and reporting workloads.
2. Does mirrored data inherit source system permissions?
No. Replicated datasets must be governed using native analytics platform access controls.
3. Why is consumption-time enforcement important?
It ensures that policies are evaluated at query execution, reducing exposure through alternative access paths.
4. How does row-level security differ from column-level security?
Row-level security filters records, while column-level security restricts access to specific attributes within a dataset.
5. How can enterprises secure AI workloads?
AI workloads should run under identity-based access controls with row-level and column-level enforcement applied at query time.