Businesses are Losing More Due to Data Breach
Data Security failures have become a common affair with organizations venturing into big data analytics. The leaders are approaching new security practices to debunk long-standing myths that compel organizations to rely on outdated and inefficient security measures. While the cloud offers unique opportunities to modernize the services and transform operations, and also comes with undeniable inherent risk.
Organizations use public cloud service providers (CSPs) without actually understanding the risks of several commercial, financial, technological, legal, and compliance issues. One of the significant threats in cloud security is a data breach that continues to grow along with the financial loss after being breached. Breaches can be simply because of lapses in security features resulting in poor data management.
According to the report “Cost of Data Breach Report 2021”, by IBM, the costliest country in a data breach was the U.S., with an average cost of $ 9.05 million, and healthcare was the most expensive industry with an average cost of $ 9.23 million. Hence, enterprises need a combination of highly secured cloud infrastructure, automated governance, remediation, and elastic solutions with 360-degree responsiveness. Enterprises must think of cloud vulnerabilities as virtual holes that could lead to serious challenges in the future.
Cloud Computing Vulnerabilities Businesses Should Prepare For
Although cloud promises more productivity to business processes, things can be perilous if enterprises overlook safety, resilience, and controls. This can expose sensitive data like clinical data, non-clinical data, personally identifiable information, and others. Hence, the following cloud computing vulnerabilities must be considered by the businesses:
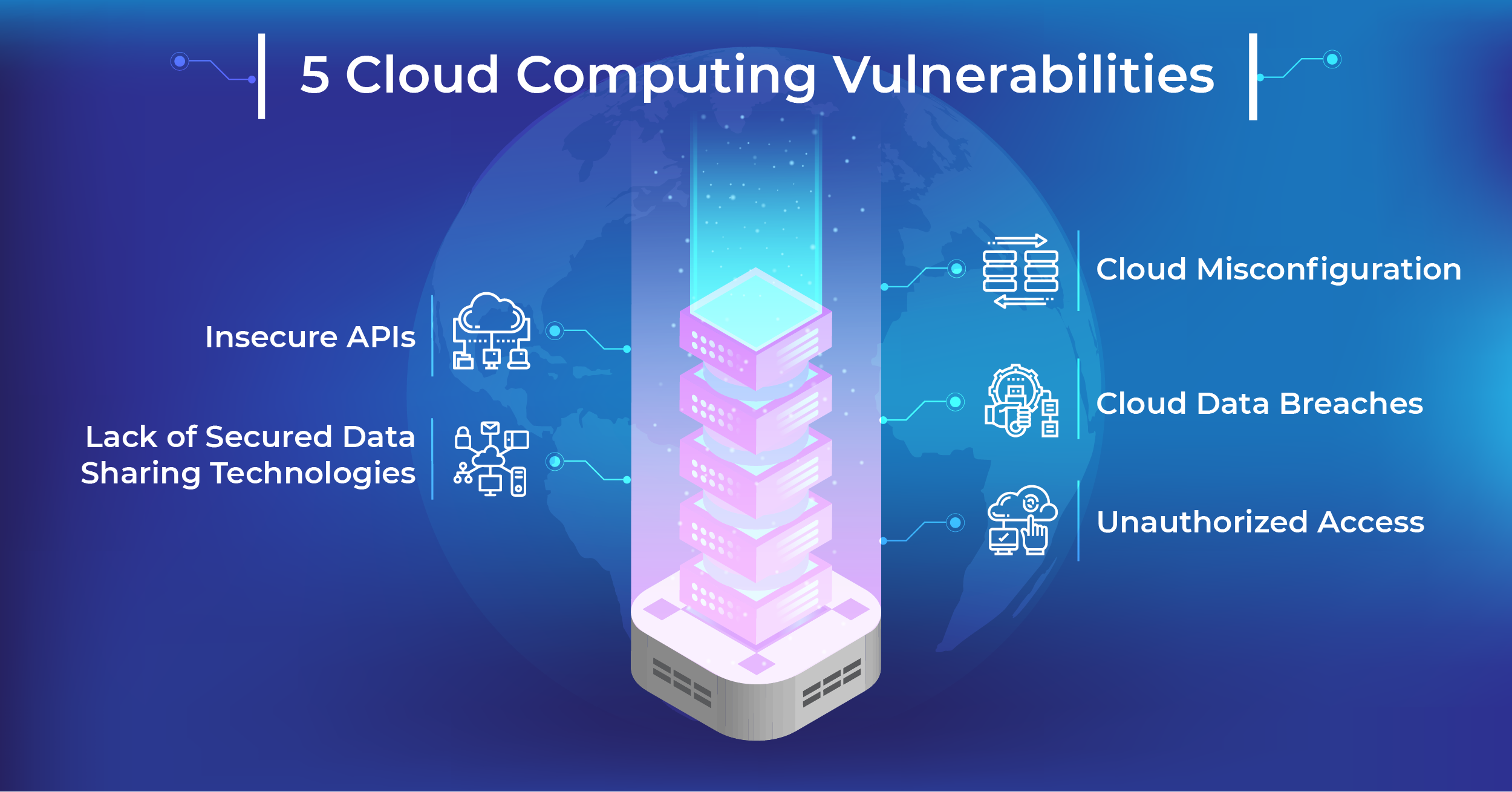
- Cloud Misconfiguration: The errors, glitches, or gaps in cloud environments that expose you to risks are called ‘cloud misconfiguration’. The cloud security risk comes from a data breach, cloud breach, or bad external actors like hacktivists, cybercriminals, etc., who leverage vulnerabilities to gain access to the network.
The “AWS security group misconfiguration” is one such example of cloud misconfiguration where an attacker can exploit flaws in AWS group configuration to access cloud server resources.
In a survey done by IDC on 300 CISOs, cloud misconfiguration threat is the one of the top vulnerabilities. Hence, double-checking the cloud configuration and using specialized tools to inspect cloud storage security settings can help combat threats.
- Cloud Data Breach: Cloud data breaches can have serious consequences, response costs, reputational damage, and even market value erosion. In this case, leadership teams must answer key questions:
- What are the ways to overcome the growing threats that come with digitization?
- Are we prepared to understand how technology investments would be affecting cybersecurity implications in the future?
- How can the gaps in resources, knowledge, and talent that outpace cybersecurity be filled?
Leaders must watch:
- How on-demand access to ubiquitous data and information is growing?
- Whether or not routine security audits are done in organizations?
- Unauthorized Access : Potentially large companies have tens of thousands of employees in the organization, increasing the chances of cloud security threat due to unauthorized access. In a survey by IDC, 83% of companies said that at least one data breach was access-related. Inappropriate security settings and stolen credentials allow outsiders to get direct access.
Identity and access management (IAM) is the security discipline that enables only the right individuals to access the resources. Formulating policies to restrict access through IP addresses would ensure that no cloud data is accessed in unsecured public clouds.
- Insecure APIs: API flaws begets threat events if it isn’t controlled in time. Insecure APIs create Issues like leaky APIs, misconfigurations, weak or broken access controls, and poor coding practices that would bring data loss, privacy impacts, privilege escalations, remote code execution account takeovers, weakened digital supply chain, and others. Attackers are evolving with time using newer ways of breaching via a complex persistent chain of attacks.
Encrypting the transmitting data with SSL is one method of protecting and profiling the accessible data.
- Data Sharing Technologies: Stores of sensitive data lying fallow in servers around the globe are now starting to generate values across enterprises, and we may expect more organizations to explore opportunities to create seamless and secure data sharing capabilities. New security issues like loss of control over sensitive data have been emerging with cloud services like Google Drive, Dropbox, etc. This fear stems from the fact that the cloud is a multi-user data-sharing environment.
Organizations need to measure the security gaps and implement their compliances rather than depending on third parties. Bringing shadow IT exposure to the cloud will relatively gain accurate picture activity and usage.
Conclusion:
Implementing “Policy as Code” Would Secure the Cloud Technologies
Cloud security is the function of infrastructural design, architecture, and the combined efforts of employees, and not just monitoring and intrusion detection. Data centers in the cloud possess the risk of network penetration and slow exfiltration of data, which becomes serious later because the damage has likely been done by the time companies detect it. So leaders must focus their attention on building, programming, and developing security while building applications from scratch.
Security infrastructure decisions must be taken care of by the security team each time the security-critical configurations are changed. Another way to do this is adopting “Policy as Code,” which will express security and compliance rules in a programming language which could be used by an application to ensure encrypted configuration.
Techment Technology provides a fully secured, highly elastic and instantly scalable data and cloud management platform that provides sustainable competitive advantage to businesses. for details, get a free consultation.
 All Posts
All Posts


