Microservices along with containers, docker, and Kubernetes have become cloud-native architecture. In microservice, an application is reduced into many smaller units or mini applications, each executing a business function. These are loosely coupled and independently deployable units which have their own stack, independent data models, and databases which make them independent of each other but communicate using APIs.
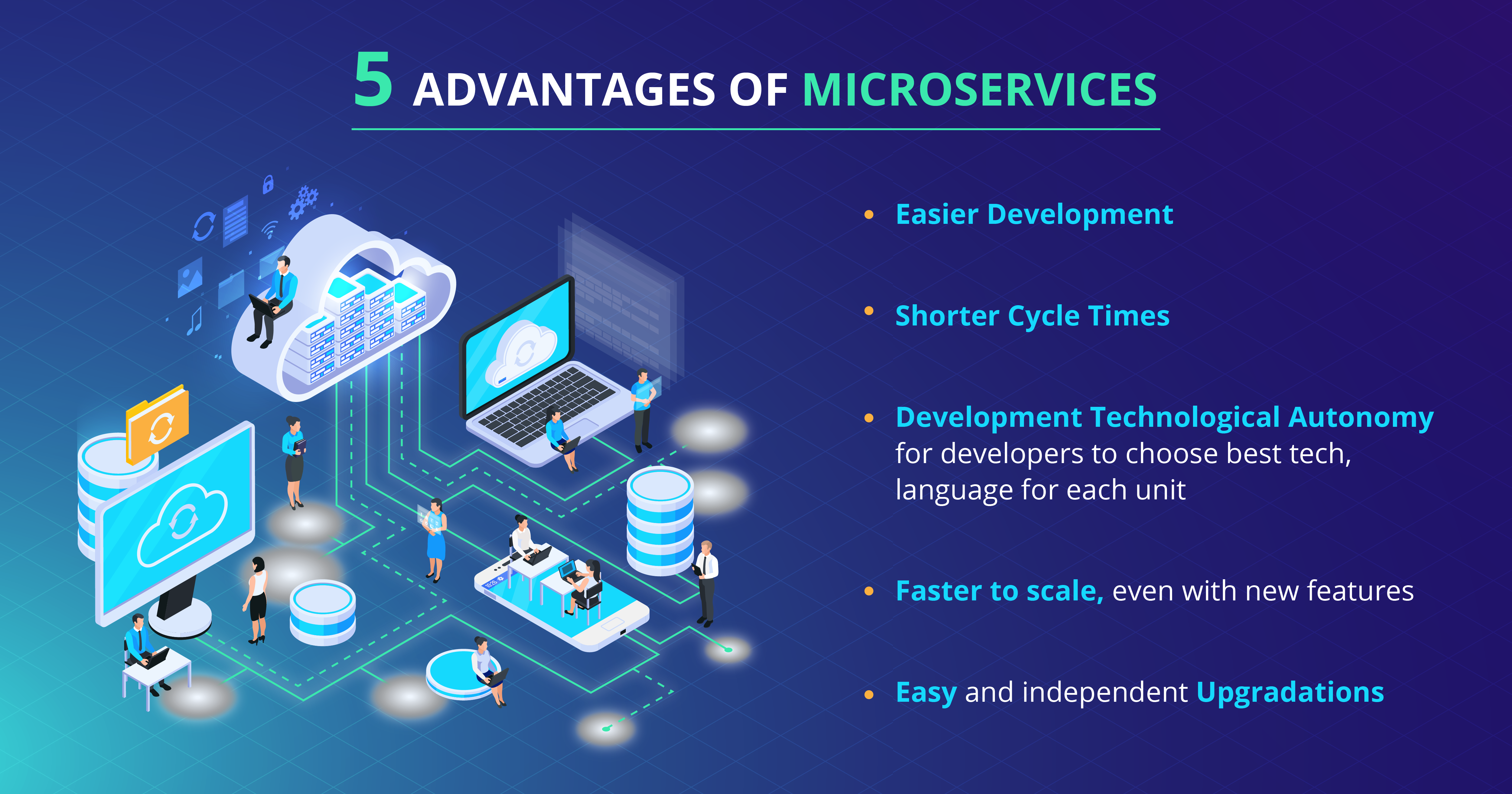
Advantages of Microservices:
- Easier Development
- Shorter Cycle Times
- Development Technological Autonomy for developers to choose best tech, language for each unit
- Faster to scale, even with new features
- Easy and independent Upgradations
Unlike a monolith application, microservices comes with the added responsibility of monitoring the application because failure of one dependent service has significant upstream performance consequences. In recent years the need for monitoring and DevOps has increased, partly due to the increased usage of microservice infrastructures.
In the last decade, the rise of microservices enabled via containerization and Docker has been astounding. According to IDC, by 2022, around 75% of global organizations will be running containerized applications in production. But as the world prepares to shift more and more applications to the cloud, via microservies, new challenges are emerging and there seems only one probable, effective and feasible solution – Anomaly Detection via AI.
Read about Microservices, containers and Docker
The Rising Challenges with Microservices
The exponential shift to microservices architecture has made the systems more distributed with east-west traffic, resulting in increasing difficulty in detecting threats and other performance issues.
Millions of applications are running across the world, with each having hundreds of microservices held in containers which are accessed from any part of the world, making their management a living albatross for enterprises to ensure uninterrupted services with reliable quality. Today, it is incumbent on enterprises how they best monitor thousands of services and maintain optimal performance and reliability.
- The increasing and ever expanding cloud expansion is making it hard to achieve the stability of the cloud ecosystem.
- Unexpected quality issues like slow access to data, web pages frustrate users; application crashes and data loss pose serious threat.
- Numerous issues make identification of critical issues impossible in real time
- The identification of critical defects among hundreds of issues in real time is now the holy grail of microservices architecture.
The Need for Automated Anomaly Detection
Anomaly detection is the domain of identification of events that deviate from the expected or permissible outcomes and are undetected by manual human supervision.
These anomalies are critical as they contain hidden significant information that is hard to find. For example, anomalous readings from different sensors could mean faulty road or weather conditions that could lead to road accidents or abnormal points from MRI images that could indicate the presence of malignant tumors.
Challenges in Anomaly Detection
The challenge with microservices is that the performance of the end microservice depends on the series of services before it, hence the delay in the initial ones causing a cascade effect. When more microservices are used, the response time increases causing performance issues in a large distributed system. The issues are diverse and so are their symptoms such as:
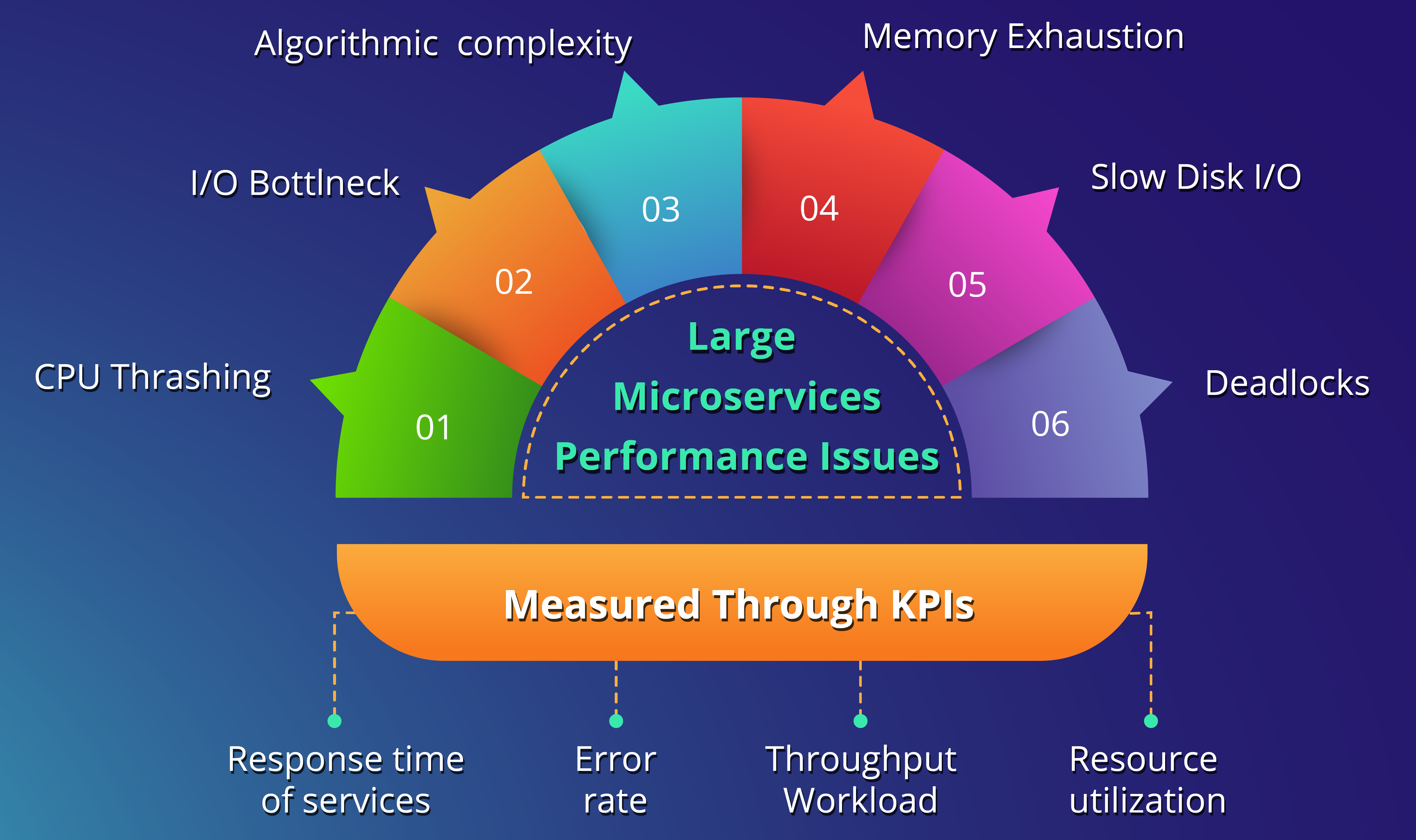
When KPIs like Error rate go undetected result in system failures which impact user experience. The problem gets further daunting as each instance (copy of service, and there are many to prevent outages) of microservice needs to be monitored, and analysis of aggregated metric is also challenging, when this is done for multiple services.
Types of Anomalies
To identify an anomaly is not a simple task, this would become clear with understanding the types of anomalies:
- Point Anomalies: A single isolated case of deviance
- Contextual Anomalies: Deviance visible only when given a context. Ex. high CPU usage with no users.
- Collective Anomalies: Deviation which becomes one when other instances are put together. They generally indicate anomalous system behavior.
The Biggest Challenge with Anomaly Detection
Subjectivity and dynamics pose great challenges; a point anomaly can become a contextual or a collective anomaly, the dynamics keeps on changing. Though it is tempting to put fixed error thresholds on what is not an anomaly and what is, but because everything is so fluid and complex, organizations must avoid using fixed approaches and instead follow a dynamic one.
Automating Anomaly Detection with AI and ML
The microservices system has become incredibly vast and overwhelming. Manual supervision can not keep pace with it. The need of the hour is AI enabled anomaly detection coupled with automated corrective action.
There are three types of monitoring modes:
- Supervised
- Semi-Supervised
- Unsupervised
AI Enabled Automation is the Future
The health of a growing microservices system depends on a large part of its flawless functioning which is key to user experience. With numerous upgrades and features, complexity increases over time, manual monitoring falls much short.
The future lies with AI-enabled supervision, under any mode, but it is crucial to prevent failures, and also that when they do occur, remedial action must be taken in real-time.
Those organizations who want to derive the maximum benefit from microservices and cloud must consider deploying AI to keep an eye on the health of their rapidly expanding and growing microservice applications.
 All Posts
All Posts